SD-WAN (Software-Defined – Wide Area Network) technology
SD-WAN technology serves to simplify the management and operations of WAN connections by separating the network hardware from its control mechanism. This technology enables companies to expand their business over long distances by connecting remote locations to their HQ. In this way, applications that run between sites, which are very important for companies’ business, can have the highest priority, with the least delay and packet losses.
Several vendors today allow the use of SD-WAN services as part of their primary service. Some of the vendors are Palo Alto, Fortinet, Velocloud, and the like.
Palo Alto SD-WAN
Palo Alto SD-WAN technology enables the use of multiple private and internet services to create a smart, dynamic WAN environment for low latency, fast response, and the availability of business-critical applications. In this way, using Palo Alto SD-WAN technology, companies can determine which applications are important to them, have the highest priority over other applications where speed, response, and latency are less important. No need to purchase additional or other special WAN services. Use pre-existing connections in a smarter way. Status monitoring for each link includes tracking delay, packet loss, and connection jitter. You can adjust applications granularly, and thus applications that are important for the business can always have the highest priority, with the most minor delays and in less than one second to go to the link with better performance.
Two problems arise using traditional WAN technology. If we have 2 links at a remote location to provide a redundant connection, one of those two links is passive. And that is the first problem. We pay for a link that we do not use, i.e., we do not use it to the fullest extent.
Another problem is when there is a problem on the active link, and there is no cancellation, that active link does not go down and does not switch to a passive link. Link switching usually depends on the status of the link, whether it is Up or Down. There is no intelligence to switching links. It requires a lot of engineering knowledge in routing and QoS technology. The SD-WAN module is integrated with the PAN-OS software, so you get SD-WAN functionality as part of the already known Palo Alto protection. This SD-WAN module works in conjunction with other PAN-OS modules such as APP-IP and User-ID. You can set up a topology in which remote locations access your cloud applications through your HQ. SD-WAN allows your remote locations to access cloud applications directly through a local ISP without loading connections to HQ. This type of connection is also called DIA connection (Direct Internet Access). There is no need to spend bandwidth from a remote location to HQ. The firewall itself can manage security at a remote location, so the central firewall has no obligation to do so. The image below represents a remote location that uses DIA links linked to the Cloud.
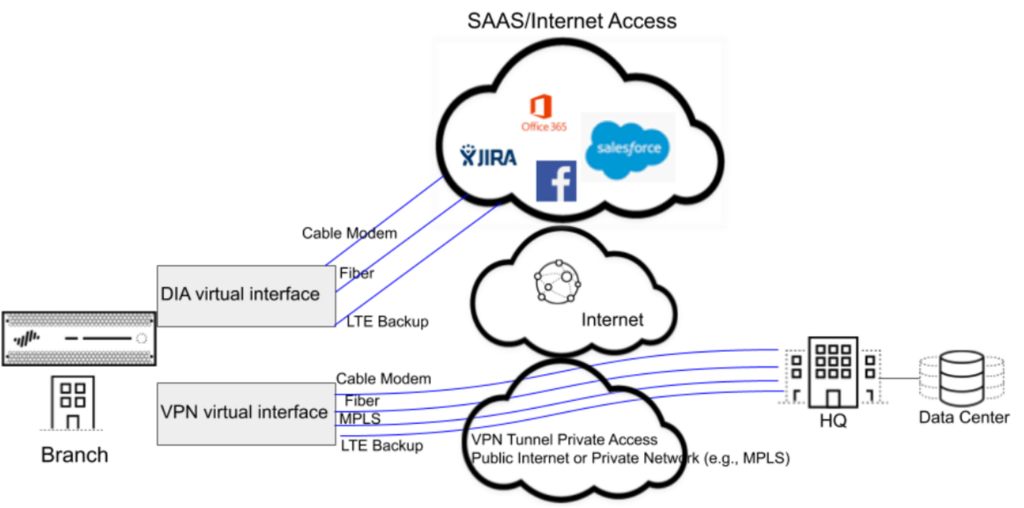
Grouping connections allow multiple physical links to go to different ISPs, merging into a single virtual SD-WAN interface. Then, based on the application and service, the firewall decides on further traffic balancing so that the highest priority applications always have the best response and speed and the least delay.
SD-WAN supports a large selection of WAN connections; therefore, it can be: ADSL / DSL, modem connection, Ethernet, fiber, mobile (LTE / 3G / 4G / 5G), radio, satellite, and MPLS connections. Naturally, you choose the best combination for the primary and backup connection.
Models currently supporting SD-WAN:
- PA-220
- PA-220R
- PA-820
- PA-850
- PA-3200 Series
- PA-5200 Series
- VM-300
- VM-500
- VM-700
Centralized management of multiple locations
Suppose your business requires a larger number of remote locations, to facilitate administration, configuration and provide better visibility of all sites. In that case, Palo Alto offers Panorama as a physical and virtual solution. Panorama is a centralized solution for monitoring and administration of all your locations and allows you to configure more SD-WAN locations faster and easier than if you did it individually for each location. The firewall uses VPN tunnels to check the status of connections between sites to detect the possibility of “cutting off” the site. To quickly configure the remote location, the best practice is to export the empty SD-WAN CSV file and enter information such as:
- the IP address of the location,
- virtual router to be used,
- location name,
- zone to which the firewall belongs,
- and information about site routing (BGP).
Prerequisites and necessary components for SD-WAN implementation:
- Minimum PanOS 9.1 with SD-WAN subscription
- Panorama with SD-WAN accessory
Configuration concept:
- Create a virtual SD-WAN interface (VPN or DIA)
- Configure Path Quality Profile (Latency, Jitter, Packet Loss)
- Create a Traffic Distribution Profile (if Path Quality exceeds maximum values)
- SD-WAN policy rule with a combination of applications, Path Quality Profile, Traffic Distribution Profile to select the best path.
There is also a solution with Prisma Access. Prisma Access is a Palo Alto security solution in the Cloud that changes your NGFW on site. By using this Cloud solution, a security solution is obtained at that location by raising security services specific to the needs of that location. Prisma Access is controlled by Panorama or Cloud Managed software. In this case, you must have Cortex Data Lake (Palo Alto Log Storage Cloud Platform).
Configure the SD-WAN on the Palo Alto firewall
Steps in configuring SD-WAN:
- Group physical Ethernet interfaces to a provider into a single logical SD-WAN interface.
- Determine the link speed
- Determine the threshold at which the existing path will be considered poor
- Specify a method to select the next better path
Configuration components:
• Tag – an arbitrary name to identify the link
o Objects> Tags (add)
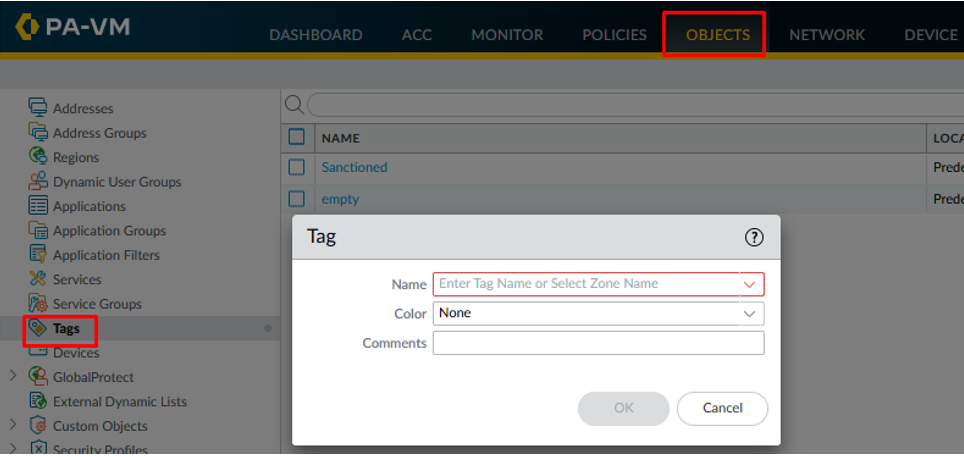
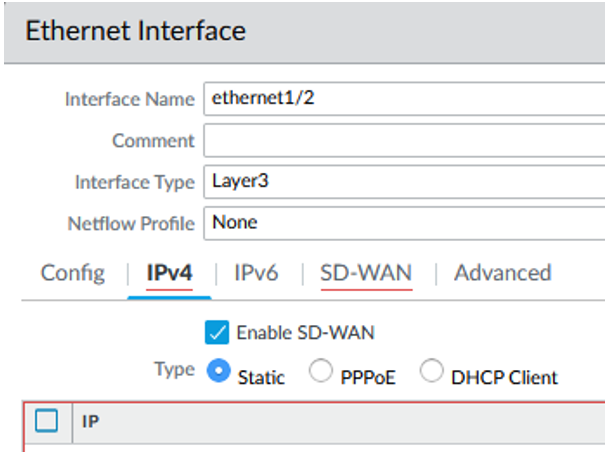
Attach the tag to the interface by enabling the SD-WAN option under the IPv4 card on the physical interface itself, and then under the SD-WAN card, applying a specific SD-WAN Interface Profile. The tag allows you to control the order in which the interfaces are used. It also gives Panorama the ability to systematically configure multiple interfaces with SD-WAN functionality.
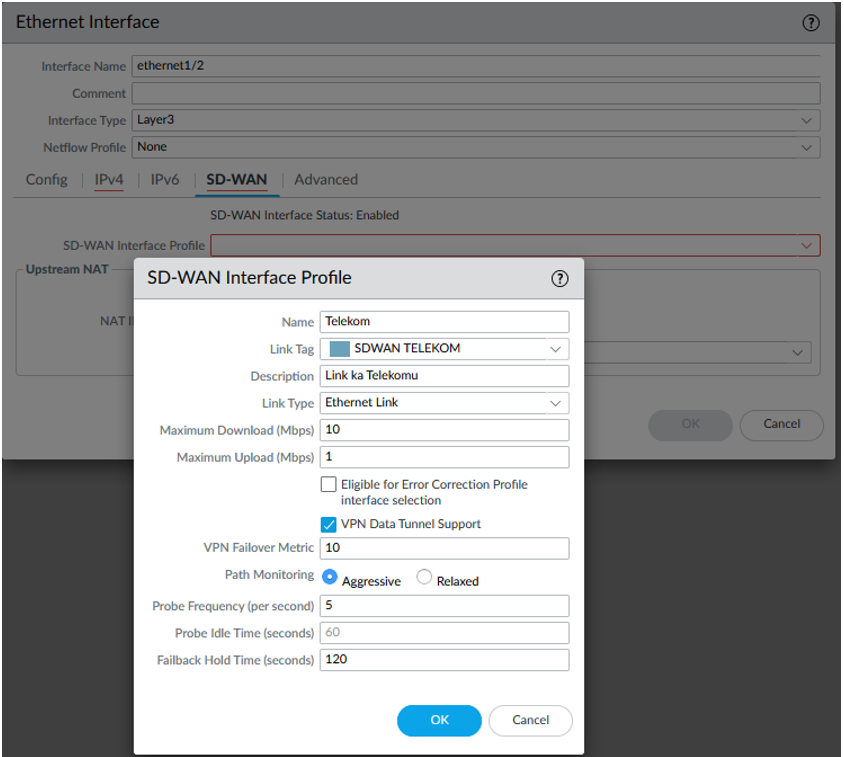
- SD-WAN Interface Profile
- Network > SD-WAN Interface Profile
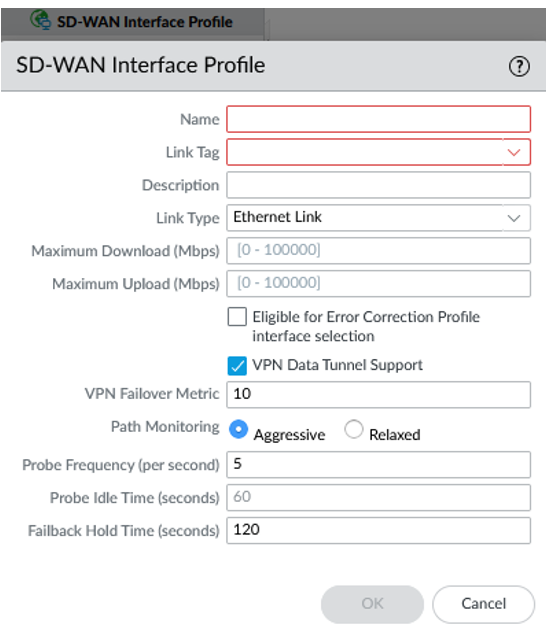
In the SD-WAN Interface Profile, you specify which tag to attach for the interface, the type of link, the maximum and minimum speed of sending and receiving to the provider, and the frequency of checking the availability of the link.
- L3 Ethernet Interfaces
- Network > Interfaces > Ethernet
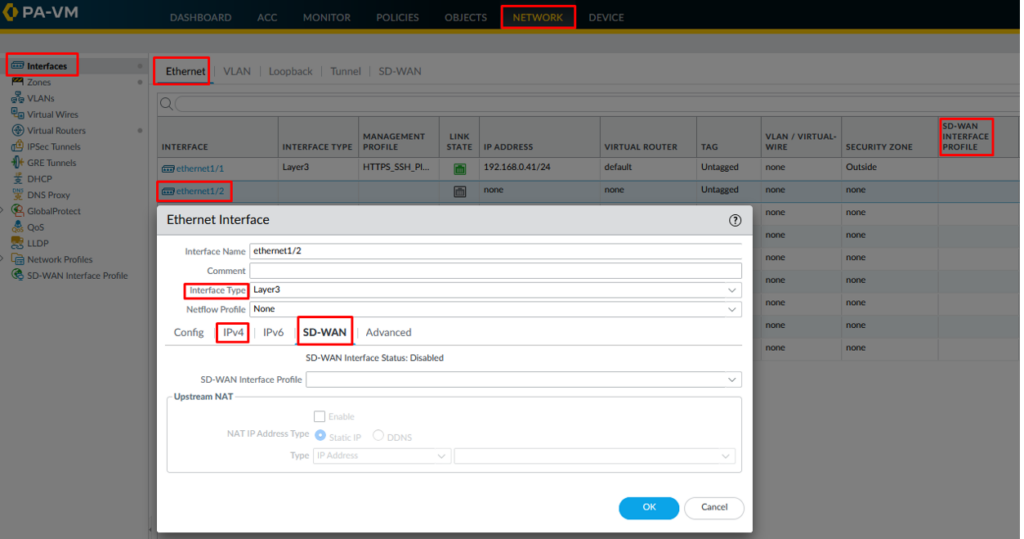
The Layer 3 interface with IPv4 address supports SD-WAN capabilities. Glue a specific SD-WAN Interface Profile to this interface to assign specific features to the interface.
- Virtual SD-WAN Interfaces
- Network > Interfaces > SD-WAN (add)
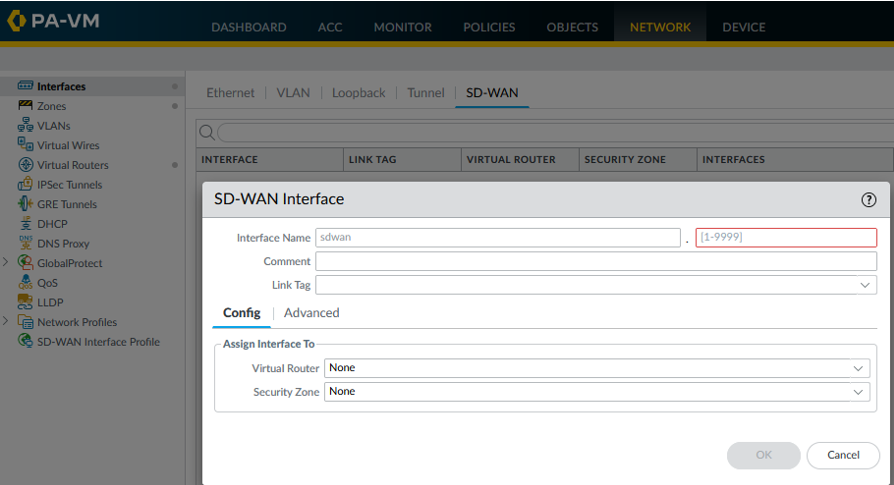
An SD-WAN interface is a VPN tunnel in which one or more interfaces are grouped into one virtual numbered SD-WAN interface to which you can route all traffic. All paths belonging to the SD-WAN group will go to the same WAN interface.
- Path Quality Profile
- Object > SD-WAN Link Management > Path Quality Profile (add)
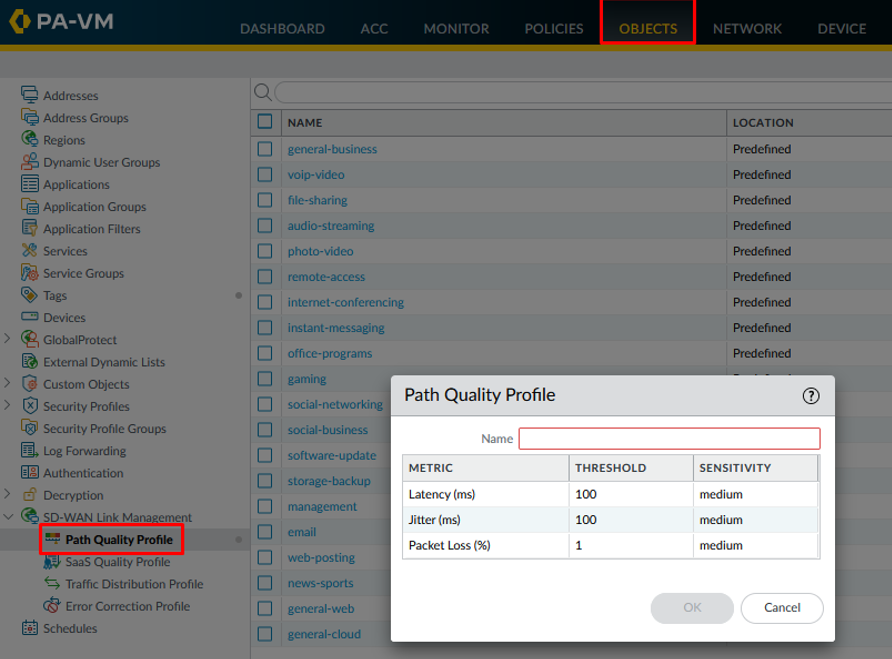
The Path Quality Profile defines the maximum delay, instability, and packet loss threshold. In the example above, crossing any threshold would mean that the firewall switches to another link.
• Traffic Distribution Profile
- Object> SD-WAN Link Management> Traffic Distribution Profile (add)
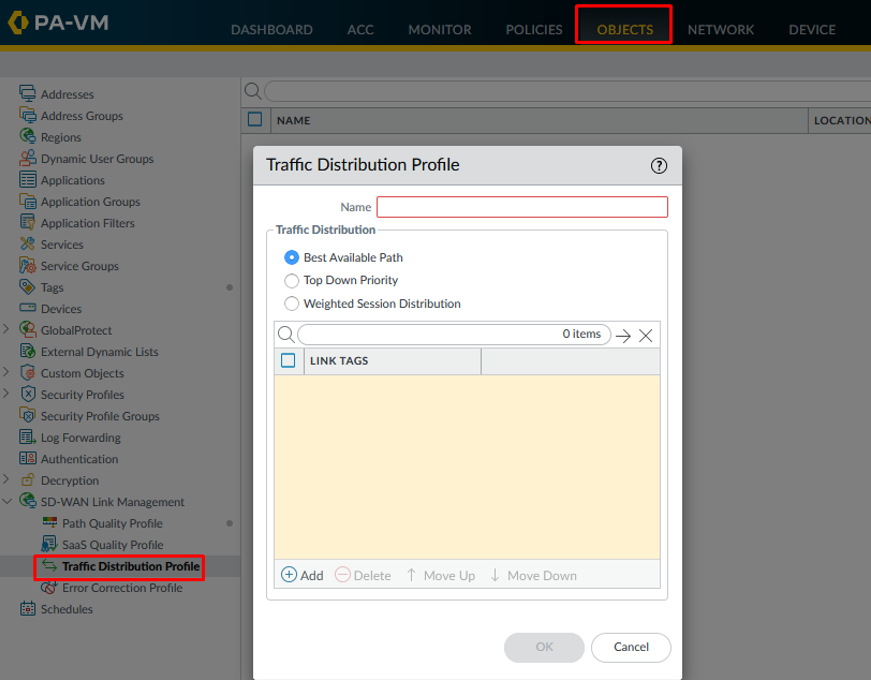
The Traffic Distribution Profile determines how the firewall will select the next best path if the current path exceeds any of the connection quality thresholds.
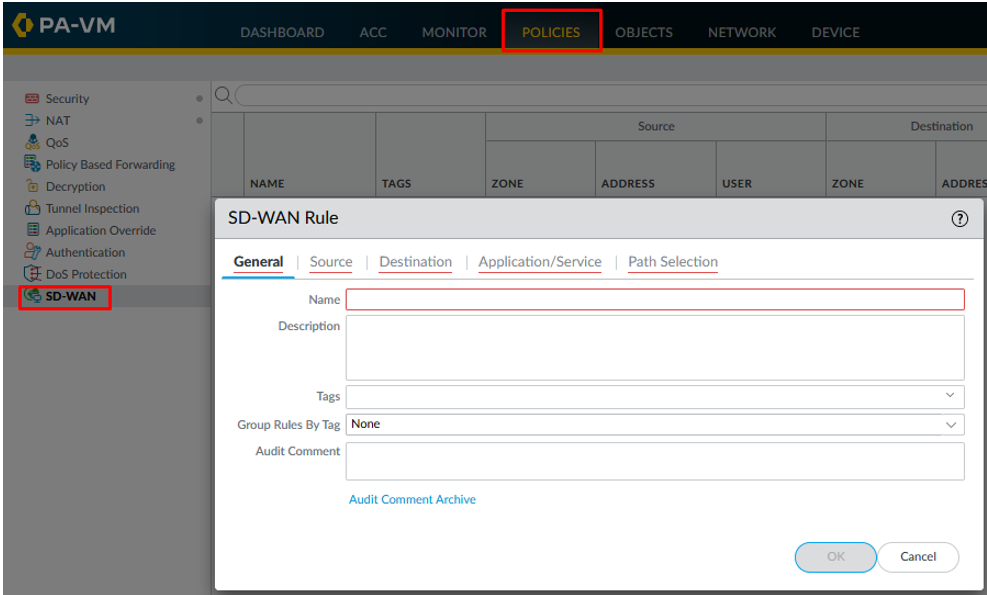
- SD-WAN Policy Rules
- Policies > SD-WAN (add)
All previously explained elements are merged into an SD-WAN policy which determines which traffic will be treated with SD-WAN technology.